Table of Contents
Preamble
So you have an Active Directory domain and you’ve installed certain services on certain computers. Now you want to allow certain non-admin users to control these services, but for obvious reasons you definitely don’t want to grant them with admin rights.
You can do this OOB via Group Policy as long as this is about a built-in Windows service, but in most cases it’s not. In this case your problem is that this third party service won’t be visible on your DC (Domain Controller) where you’d edit the GPO (Group Policy Object) because that particular service is not installed.
So at this point most tutorials would either tell you to install that service on the DC or to perform some one-time hack on that specific computer with SubInACL or whatever tool. The former idea is evil and you want to avoid that at all costs because you absolutely don’t want to increase the attack surface and instability of a DC with any 3rd party bullshit. The latter idea is good as a quick workaround but it’s not scalable and you’ll most likely forget about it when you try to figure out 2 years later why that service works on comp A and doesn’t on comp B.
So instead of messing around, let’s do this the proper way: create a security group, then grant this group control rights to a specific service via Group Policy.
Server-side
Log in to your DC. Open Active Directory Users and Computers (dsa.msc) and create a security group for the users who’ll be allowed to control that service. Then open Group Policy Management (gpmc.msc) and create a GPO. Set up its security filtering and linking according to your environment and the group you created previously, then you’re ready.
Client-side
You can do this on any computer that’s capable of running the service in question. First of all, you need to install a package called Remote Server Administration Tools. Here’s a bunch of versions of it, google for other versions:
Installing this will probably trigger a few new updates to be available via Windows Update. It’s a good idea to install them before proceeding.
Also install the service you want to define rights for so that it’ll be visible in the group policy editor.
Now start the MMC (Microsoft Management Console) as a domain admin:
runas /user:YOURDOMAIN\administrator mmc
Go to File / Add/Remove Snap-In… (Ctrl + M) and add the Group Policy Management Editor. It will open up the Select Group Policy Object wizard. Click Browse…, and select the GPO you created.
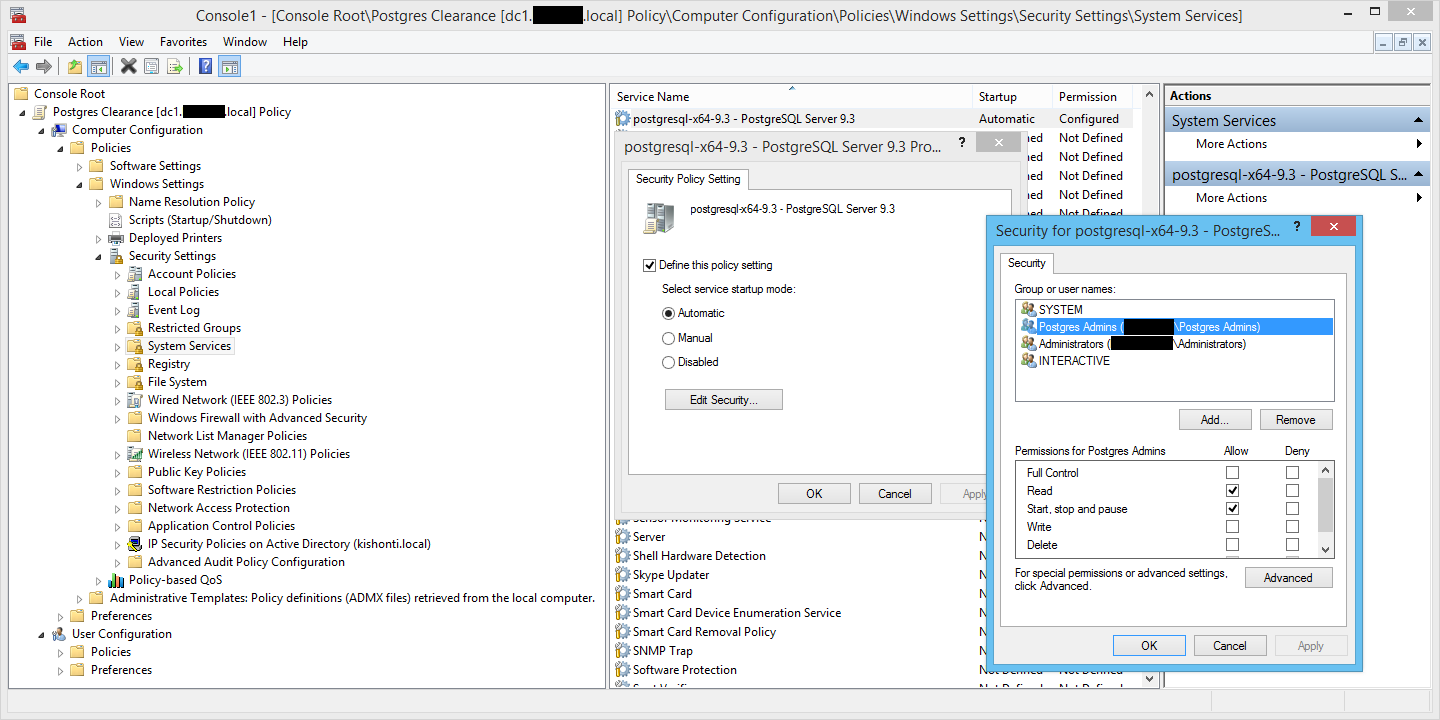
Once done, you’ll have a regular group policy editor console. Navigate to Computer Configuration / Policies / Windows Settings / Security Settings / System Services, select the appropriate service and edit its security settings according to your needs.
Now go to the computer which will actually run this service and run the gpupdate /force command.
Usage
Once a user’s added to the security group you created, she can control this service right from her workstation. Because the security token which defines group membership is only applied upon login, she may have to log off and log back in first. Then open a command prompt and do something like this:
sc \\dbserver start postgresql-x64-9.3
This example will start the postgresql-x64-9.3 service on the dbserver computer. For other commands, run sc without arguments, it will print its help by default.