Table of Contents
Basics
For the fundamentals of how SSH key pairs works, please read understanding public key private key concepts.
TLDR you put your public key on the remote machine (server) you want to manage, and you authenticate with the private key you have on your local client machine.
Generation
We use PuTTY to generate and use SSH keys, namely:
- PuTTY – SSH client
- Pageant – SSH authentication agent
- Plink – connector between Pageant and PuTTY
- PuTTYgen – key generator
Use a dedicated pendrive for storing your keys. Do not store keys on your hard drive, unless your computer’s disk is encrypted using BitLocker. Start PuTTYgen, select the ED25519 key type, then click Generate.
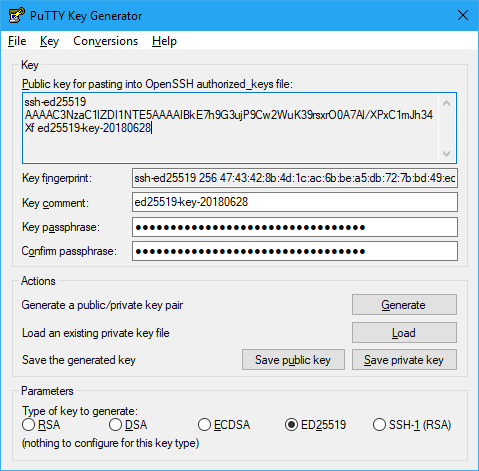
Make sure to specify a Key passphrase. then save the following 3 files on your pendrive:
| Save as | UI Action | Description |
|---|---|---|
id_ed25519.ppk |
Save private key | Private key in PuTTY format |
id_ed25519 |
Conversions / Export OpenSSH key | Private key in OpenSSH format |
id_ed25519.pub |
Public key for pasting into OpenSSH authorized_keys file | Public key in OpenSSH format |
Public Key on the Remote Server
Log into the remote machine with PuTTY using your username + password, and perform the following:
mkdir -p ~/.ssh
touch ~/.ssh/authorized_keys
chmod 700 ~/.ssh
chmod 600 ~/.ssh/authorized_keys
If this host has SELinux enabled (Ubuntu doesn’t have SELinux, while RHEL/CentOs does, by default), also do:
restorecon -rv ~/.ssh
Then paste the contents of id_ed5519.pub into ~/.ssh/authorized_keys and save.
You have to do this only once.
If you’re in doubt, use mc, which is a command-line file manager and text viewer, it should get you started. You might have to install it first:
sudo yum install mc
Private Key on the Local Client
Start Pageant and load id_ed25519.ppk. You have to do this after every reboot. To minimize the number of times you need to do this, it is recommended to hibernate your workstation instead of shutting it down.
After finishing the steps above, you should be able to log in without entering your password.